
Saving a top 3 telecoms provider £1 million by preventing streaming account theft
Download Case StudyCustomer profile
- Top 3 telecommunications provider with over 15 million customers
- Serves fixed-line, broadband and mobile services, as well as subscription TV packages
- Customers have access to premium multimedia streaming services
Results
- £1 million saved by reducing customer support calls
- On average over 1,000 and a peak of over 500k malicious login attempts blocked per hour
- More than 350,000 account takeover attempts using stolen login details blocked in less than a year
The challenge
The client is one of the top three largest multinational telecommunications companies based in the UK, with over 15 million customers.
Their customers can access streaming media services, such as Netflix, Spotify and Apple TV, included in their broadband and television subscriptions or as an add-on. These are bundled as part of partnership agreements with the content providers.
Bundled streaming services targeted by criminals
These desirable assets made the business a frequent target for credential stuffing attacks. Netacea’s Threat Research team found numerous credential stuffing configuration files on the dark web specifically written to target the client. Attackers used automated bots to validate credentials leaked from other sites on the client’s authentication service.
Once they gained access to the accounts, hackers would then sign up to the bundled streaming services via the telecommunication business’s customer portal and sell the streaming account details on the dark web for a profit. Our Threat Research team uncovered hundreds of stolen accounts on sale for as little as £3 each.
A strain on time, resource and partnerships
The impact of these account takeover attacks was wide reaching, requiring meetings across the client’s fraud and security teams to triage. The malicious activity also created a backlog of support calls from frustrated customers who were locked out of their stolen accounts or had been charged for streaming services they never signed up for.
The issue was also damaging the business’s reputation with media streaming partners, who were frustrated that their services were being stolen, requiring their action to repatriate or cancel accounts.
Initial investigation: highly distributed attack
The business initially asked Netacea to investigate historic data from a two-day period. From the investigation, Netacea uncovered highly distributed malicious traffic attacking their login pages:
- 18% of all login requests made by malicious bots
- Bot attacks distributed across 11,000 IP addresses, 1,500 data centers and 100+ countries
- 470,000 login attempts by bots across the two-day period
Based on these findings, the business engaged with Netacea to implement live analysis on real-time traffic in an ongoing engagement.
The solution
Netacea worked closely to integrate into the authentication service for all the client’s sites, apps and APIs, covering all potential bot attack vectors. Netacea investigates each request made on the platform, comparing every data point to distinguish between humans, benign bots and malicious bots. This allows for instant recommendations on whether to permit, challenge or block traffic.
Adapting to new and changing attacks with AI
Previous attempts by our client to block bot activity had limited success. The bot operators quickly identified rule-based blocking methods and found new ways to bypass defenses.
Netacea’s next generation bot management technology, Intent Analytics®, detects complex attacks by using a combination of machine learning approaches that are invisible to attackers.
Firstly, we feed every user interaction into supervised machine learning models, which flags any users who are behaving in the same ways as other known malicious users and can predict when attacks will occur based on previous patterns.
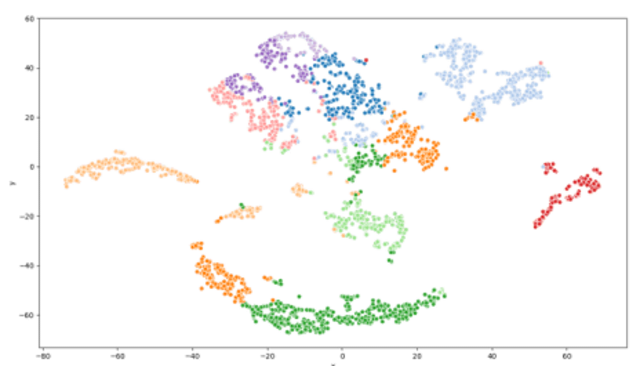
Then we detect emerging or changing threats using unsupervised machine learning algorithms. Without predefined labels or human intervention, these models group users into continually reevaluated clusters based on their behavior.
This means that Netacea continually improves its bot detection technologies with each new attack type used against our clients, keeping them ahead of their adversaries.
The outcome
Over a period of nine months, Netacea has mitigated an average of over 1,000 malicious login attempts per hour across the client’s website, apps, and API. This peaked at over half a million attempts per hour during the most aggressive volumetric attack.
By preventing over 350,000 user accounts from being stolen, and assuming a 10% call-in rate, Netacea has saved the client potentially £1 million to date in calls to their customer support call center alone, without taking into account the cost of investigation, analysis, refunds, and reputational damage.
More importantly, the client’s customers are now protected against account theft. This removes disruption to their services, which is a key deliverable for the business, and allows the client to focus on their goal of improving the lives of their customers.
Subscribe and stay updated
Insightful articles, data-driven research, and more cyber security focussed content to your inbox every week.
By registering, you confirm that you agree to Netacea's privacy policy.